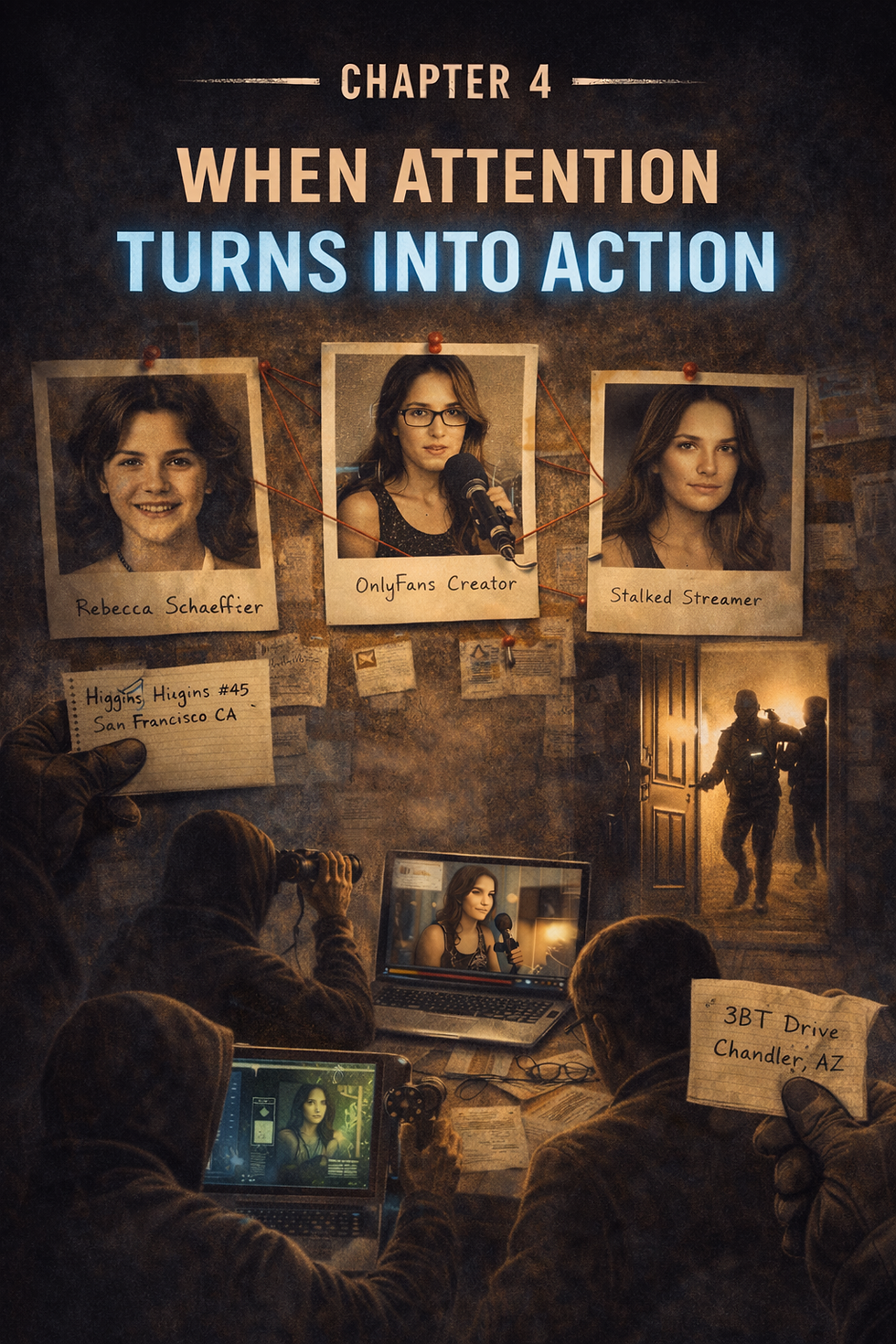
Chapter 4: When Attention Turns Into Action
- Feb 27
- 4 min read
Chapter 1: The Day You Become Searchable
Most of what we’ve talked about so far happens quietly.
Someone watches.
Someone pays attention.
Someone connects details over time.
Most of it never turns into anything.
But sometimes it does.
Not all at once.
Just enough to move from observation… into action.
When Information Becomes Real
There’s a point where curiosity stops being passive.
Something gets confirmed.
A name.
A location.
A routine.
Once that happens, the distance between online and real life starts to shrink.
And when that distance closes, behavior changes.
This isn’t new.
It’s just easier now.
When Access Comes From the Inside
Long before social media, access to personal information created the same kind of risk.
Rebecca Schaeffer was a young actress in the late 1980s. A man who had become fixated on her obtained her home address through a private investigator. The investigator accessed motor vehicle records and provided that information.
There was no hacking.
No advanced method.
Just access—through someone who had it.
What followed wasn’t complicated.
He went to her home and killed her.
That case led to major changes in privacy law, including restrictions on access to motor vehicle records.
But the underlying problem didn’t disappear.
It changed form.
The Same Pattern—Different Sources
Today, most creators are leaving digital trails. But, it is still true that someone can dupe a private investigator into giving them information. Perhaps not even through trickery but from the PIs desire to make money, could lead to a nefarious person obtaining private information.
The digital trails are far more opportunity for the average psychopath.
Patterns.
Connections.
Fragments that can be assembled.
Different method.
Same outcome.
Targeted Home Invasion of a Creator
In 2025, a well-known online creator and OnlyFans personality was targeted in a violent home invasion.
Three armed individuals entered her home at night while she was inside.
They weren’t guessing.
They were looking for cryptocurrency she had publicly discussed.
She was assaulted and forced to give access to her accounts.
This wasn’t random.
It was targeted.
The information wasn’t hidden.
It was visible—and interpreted as accessible.
The “Stalker in the House”
In another widely reported case, a man became fixated on an online creator he had interacted with.
He didn’t threaten her.
He didn’t force immediate contact.
He escalated quietly.
He entered her home without permission.
More than once.
He hid inside.
At one point, he remained inside long enough to observe her routine and eventually entered her bedroom while she slept.
This didn’t begin as a violent event.
It began with attention.
Then familiarity.
Then access.
By the time it became obvious, it had already gone much further than most people think is possible.
Repeated Stalking of a Major Creator
A high-profile content creator and streamer has dealt with multiple stalking incidents over several years.
In one case, an individual traveled long distance after becoming fixated through her content.
In another, someone attempted to access her home while she was away.
Different people.
Same behavior.
The content created familiarity.
Familiarity created perceived access.
And for some individuals, that was enough.
Swatting and Real-World Consequences
Swatting has become a recurring issue for online creators.
False emergency calls are made, sending armed law enforcement to a creator’s home.
These incidents don’t require proximity.
They require one thing.
An address.
Once that information is known—or believed to be known—it can be used to trigger a real-world response.
In some cases, these events have resulted in serious injury or death.
Not because of the creator.
Because of the response to false information.
Targeted Theft and Surveillance
In another recent case, an OnlyFans creator’s home was targeted for a high-value burglary.
The individuals involved appeared to know when the home would be empty and what valuables were likely inside.
This wasn’t opportunistic.
It was informed.
Information had been gathered over time.
Not from a single source, but from patterns.
Visibility.
Routine.
What These Cases Have in Common
Different people.
Different platforms.
Different outcomes.
Same structure.
Someone becomes aware of the creator.
That awareness turns into interest.
That interest turns into information gathering.
And eventually, that information becomes usable.
Not everything.
Just enough.
The Escalation Pattern
It doesn’t jump from zero to extreme.
It builds.
Observation becomes familiarity.
Familiarity becomes assumption.
Assumption becomes action.
Each step lowers the barrier to the next.
And by the time something physical happens, it’s not the beginning.
It’s the continuation of something already in motion.
The Misunderstanding
Most creators assume this requires:
Technical skill.
Advanced tools.
A coordinated effort.
It usually doesn’t.
It requires:
Time.
Consistency.
And enough information to connect.
That’s it.
Why Creators Are Different
Traditional public figures had distance.
Layers.
Representation.
Separation.
Creators don’t.
They are the brand.
They are the access point.
They are the connection.
That’s what makes growth possible.
It’s also what creates exposure.
Because familiarity, when misinterpreted, becomes perceived access.
And perceived access leads to real attempts at access.
What This Should Change
This isn’t about fear.
It’s about clarity.
These cases aren’t rare exceptions.
They are visible versions of a pattern that exists at smaller levels every day.
Unwanted contact.
Escalation.
Boundary crossing.
Most of it never reaches headlines.
But it follows the same path.
The Real Question
The question isn’t:
“Could this happen?”
It’s:
“What would someone need to make it happen?”
Because once you understand that, you stop thinking in isolated posts.
And start thinking in structure.
Where This Goes Next
Now we move into something more practical.
Where exposure actually happens.
Not the obvious places.
The small ones.
The routine ones.
The things that feel harmless—until they connect.
Because once you understand where the gaps are, you can start closing them.
Closing Thought
Most people don’t act without a reason.
But they don’t need much of one.
Sometimes all it takes is:
Access plus opportunity and something that connects the two.




Comments